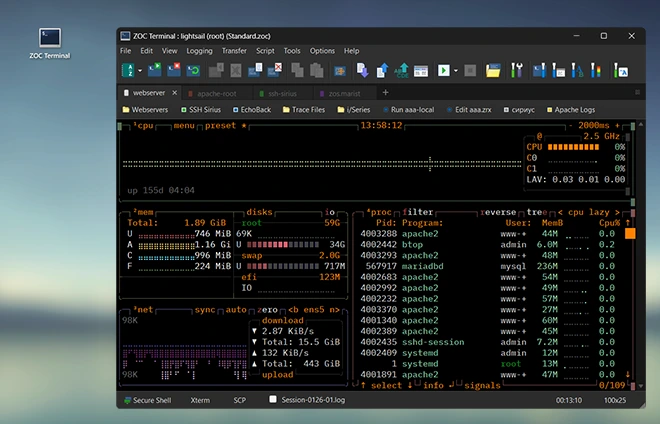
is wrapped in a modern tabbed user interface with a powerful
host directory, industrial strength emulations and scripting.
Below is an overview and explanation of some core SSH features of ZOC Terminal. We also have a whitepaper
offering a more technical description of SSH.
Authentication
Authenticating describes the process, where the user presents proof of who he is and
the server deciding, if the user should be allowed access. The SSH protocol describes
various methods that can be used for authentication.
Of those, ZOC supports password authentication, public-key exchange and keyboard-interactive challenge.
Public-key exchange comes in various flavors. ZOC understands RSA, DSA, ECDSA and ED25519 keys.
Hardware (smart card) based key authentication is also possible.
Encryption
Over time, the SSH protocol has seen a plethora of methods to be used to encrypt the
communication (using shared secret was negotiated during the KEX phase as a cryptographic key).
Some ciphers were phased out over time, especially after Edward Snowden revealed how powerful possible
listeners like the NSA are, and new ones were introduced. ZOC supports the whole list,
starting with aes256-ctr and going down to older ciphers like aes256-cbc or arcfour
(these older ones may still be necessary to connect to
older servers which have not been updated in a while).
Dynamic Port-Forwarding
The standard port-forwarding feature requires the client to set up the tunnel source port and
destination before making the connection. This means that there is limited flexibility and
that for each possible destination, a separate ssh tunnel needs to be set up.
With dynamic port forwarding however, the client sets up a listening port, but when a software
connects to the port, it can select host and port it wants to connect to. The ssh client
will then forward the connection request to the SSH server which initiates the connection
to the final destination.
SSH Connection via Proxy
In some environments, end user computers are not allowed to access the outside internet directly.
In those cases, connection and data exchange is made by way of a
ssh proxy which handles the actual
connection to the outside network (internet). There are various type of proxies, which mainly
differ in how the requests
a connection to the outside world. Most common types are
SOCKS-4, SOCKS-5 and
HTTP.
ZOC supports connections through those types, as well as connections
made through ssh-jumpservers.
SSH Agent Forwarding
When a user authenticates an
SSH v2
session using a public/private key pair, ZOC supports the
SSH agent forwarding
technique to provide the key for authentication in secondary ssh sessions
(ssh connections to a third server, made from typing a ssh command in the remote shell in
the initial connection). If all the servers allow authentication through this specific ssh
key pair, it is not necessary to provide the passphrase again for secondary ssh connections.
X11 Forwarding
X11 is a communication protocol which allows a remote computer to run programs with a graphical
user interface on a remote computer (normally,
the remote computer can only show text in a
terminal client).
SSH supports a way to tunnel this type of communication between ssh client and
server, thus enabling the user to run an X11 command like xeyes on the remote shell and get the
window for that displayed on the local computer.